Fusion Node 942395840 Cyber Pulse

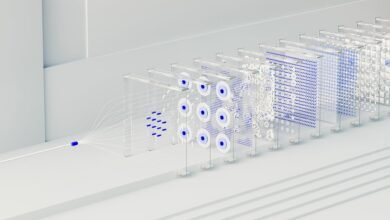
Fusion Node 942395840, branded as Cyber Pulse, represents a significant advancement in cybersecurity solutions. This system integrates robust user authentication, advanced threat detection, and real-time analytics, addressing the complex challenges organizations face today. Its sophisticated algorithms not only identify vulnerabilities but also provide immediate insights into potential risks. As the landscape of cyber threats continues to evolve, understanding the implications of Cyber Pulse becomes crucial for organizations seeking to maintain data security and user trust.
Key Features of the Cyber Pulse
The Cyber Pulse, designated as Fusion Node 942395840, boasts a range of key features that enhance its operational efficacy in cybersecurity domains.
Notably, its robust user authentication mechanisms ensure that access is strictly regulated, safeguarding sensitive information.
Additionally, advanced threat detection capabilities enable proactive identification of potential vulnerabilities, allowing organizations to respond swiftly to emerging risks and maintain a secure digital environment.
Advanced Algorithms and Real-Time Analytics
Advanced algorithms underpin the Cyber Pulse’s effectiveness, enabling sophisticated data analysis and threat assessment.
Through real-time processing, these algorithms facilitate immediate insights into potential vulnerabilities, while predictive analytics anticipate emerging threats.
This combination enhances decision-making capabilities, allowing users to respond proactively to cyber risks.
The integration of advanced methodologies ensures that organizations can maintain resilience in an increasingly complex digital landscape.
Enhancing Data Protection and Management
Building upon the insights generated by advanced algorithms and real-time analytics, effective data protection and management become paramount in safeguarding sensitive information.
Implementing robust data encryption techniques ensures that unauthorized access is thwarted, while stringent access controls dictate who can interact with critical data.
This dual approach not only enhances security but also fosters a culture of trust, empowering individuals to confidently manage their data.
Future Implications for Cyber Security
How might the landscape of cyber security evolve in the coming years as technology continues to advance at a rapid pace?
The advent of quantum computing poses significant challenges, necessitating robust strategies for regulatory compliance.
Organizations must adapt their frameworks to safeguard against unprecedented vulnerabilities while fostering a culture of innovation that prioritizes user freedom, transparency, and resilience in the face of emerging threats.
Conclusion
In an era where cyber threats loom larger than ever, Cyber Pulse stands as a formidable bulwark against potential breaches. Its advanced algorithms and real-time analytics not only enhance data protection but also empower organizations to navigate the complexities of cybersecurity with unparalleled agility. As technology continues to evolve, the implications of Cyber Pulse are profound, positioning it as an indispensable tool for fostering user trust and fortifying digital environments against the relentless tide of cybercrime.